Since 2023, Match Systems has handled over a hundred investigations involving address poisoning – ranging from a few thousand to hundreds of thousands of dollars in losses. In 2026, cases are arriving in dozens. Over that period, the company’s analysts have watched the attack evolve from manual fraud into a fully automated pipeline, shift its primary blockchain, and build a resilient laundering infrastructure. This article draws on Match Systems’ operational data: real recovery statistics, a typical stolen-funds routing path, and the factors that determine the outcome in any given case.
Not a New Threat – a New Infrastructure
Address poisoning has been operating at scale since 2023. What has changed is not whether the attack exists, but where and how it plays out.
In 2024 the primary battleground was Tron. The reason was straightforward: USDT-TRC20 dominated transaction volume, and network fees were so low that dust broadcasts to thousands of addresses cost fractions of a cent per transaction. Industrial-scale attacks were economically trivial.
In 2025-2026 the center of gravity shifted to Ethereum. The trigger was the Fusaka upgrade, which pushed fees down to tens of cents and made the network comparable to Tron in attack operating cost. According to independent on-chain research, new address creation grew 2.7x relative to the 2025 average – and 67% of new addresses received a dust transaction as their first network interaction. In January 2026, Citi analysts explicitly flagged a record surge in sub-$1 transactions as a marker of an active poisoning campaign. The FBI officially warned about the growth of such attacks as far back as April 2024, noting that they are equally effective against experienced and novice users – because they exploit habit, not ignorance.
The shift is clearly visible in Match Systems’ caseload: while the majority of 2024 referrals involved Tron, a significant share of new cases in 2026 arrives via Ethereum.
Why This Is No Longer Manual Work
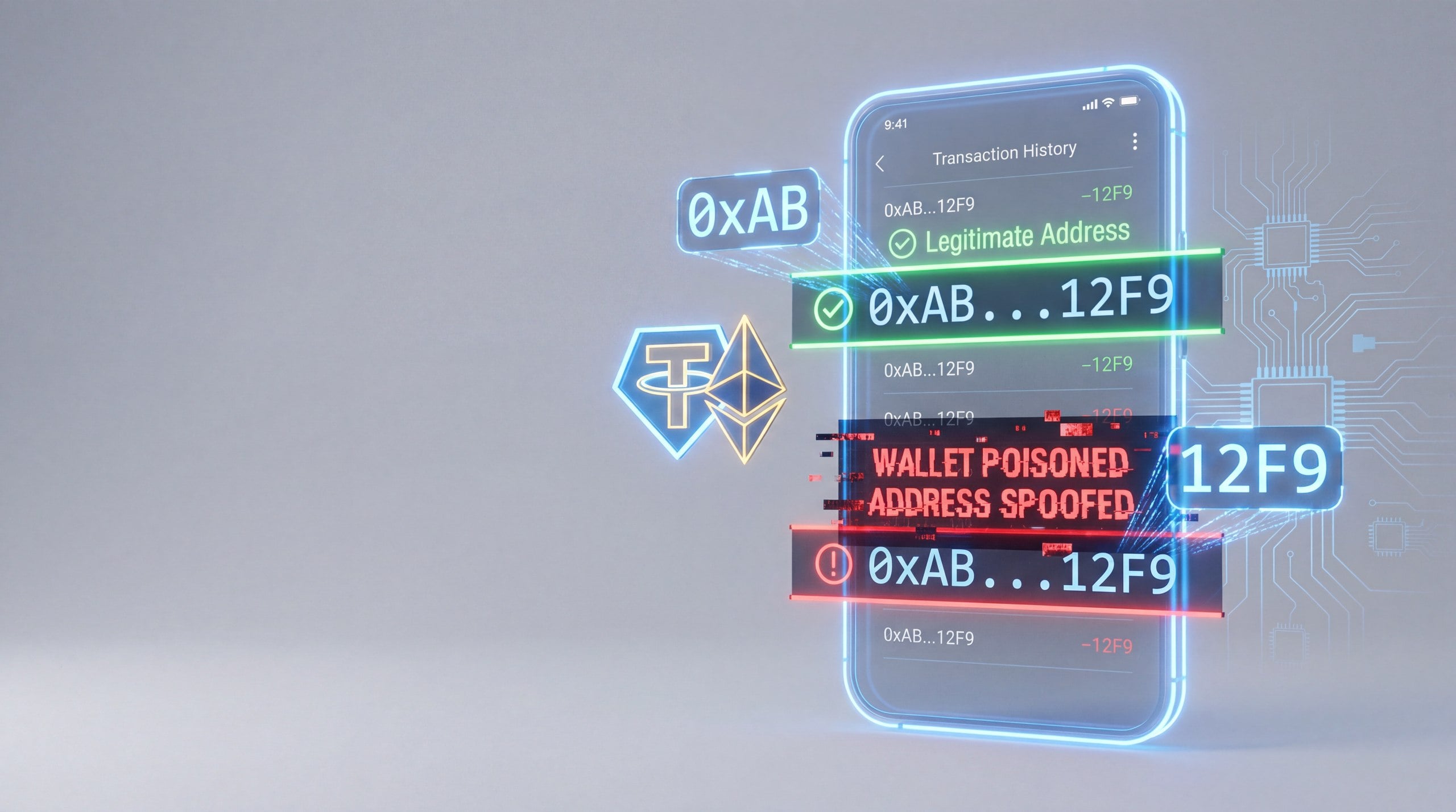
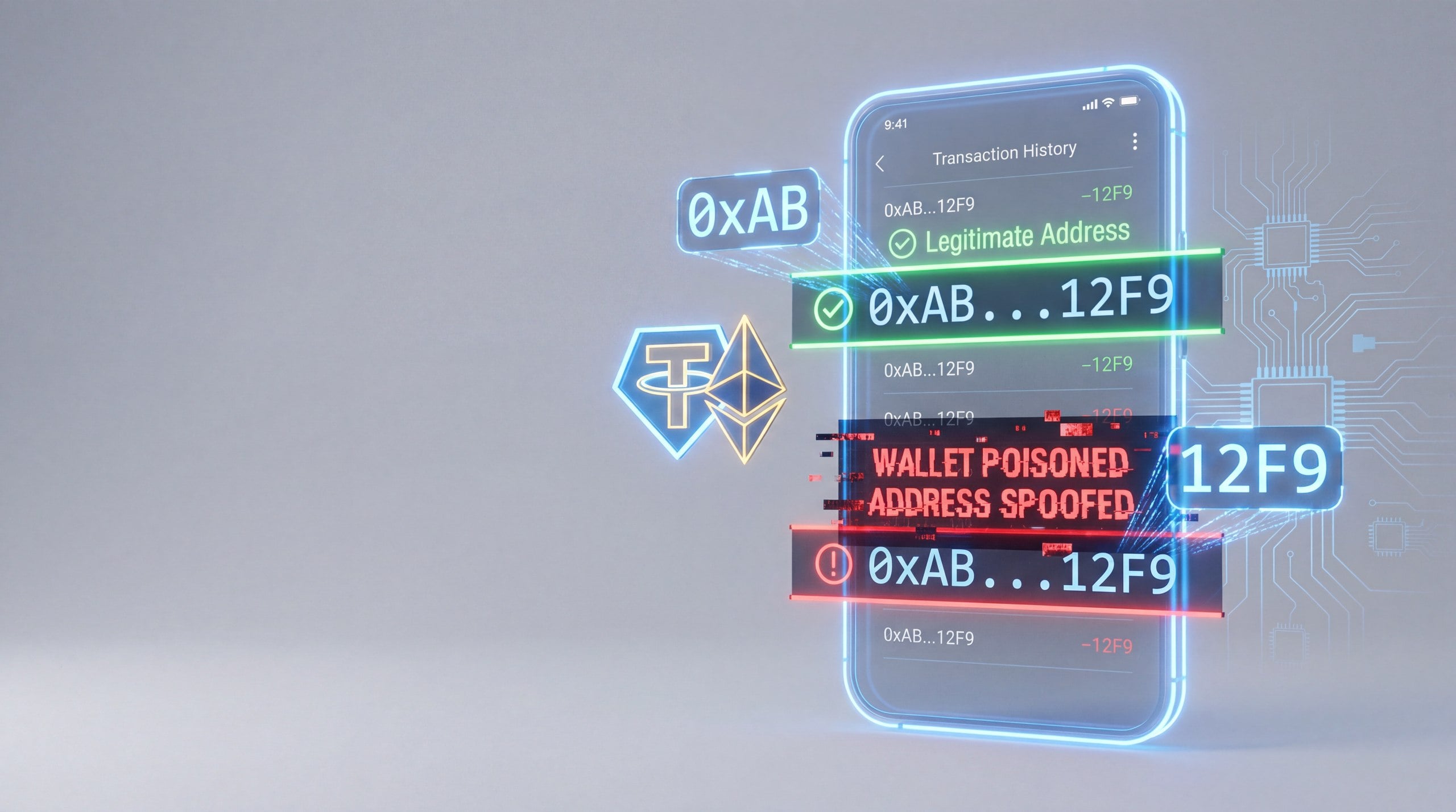
The nature of the modern attack matters. This is not a fraudster manually hunting for a victim. It is an automated pipeline.
Smart contracts fan-fund hundreds of poisoning addresses in a single transaction – researchers have documented contracts that supplied gas to hundreds of attacking addresses and financed millions of dust broadcasts in one operation. Bots continuously scan the blockchain, select active wallets with large balances, generate lookalike addresses matching the first and last characters of the target, and fire dust. The entire stack is sold on Telegram as a ready-to-use service.
Solo actors exist in this segment, but the bulk of financial damage comes from organized groups. This fundamentally changes the investigation picture: such groups maintain stable infrastructure – hub addresses from which assets are distributed to attacking wallets. Those hubs are the analyst’s primary leverage point. Some are already publicly labeled in blockchain explorers, and it is precisely through cluster analysis and on-chain linkage that attribution and address labeling become possible.
The Laundering Route: a Closing Window
Understanding the typical routing path is critical – it determines whether a response is feasible at all.
On Tron in 2024, stolen USDT-TRC20 was converted into the network’s native token, split across transit wallets, and exited to fiat via P2P platforms or Asian OTC desks. The conversion served a specific defensive purpose: the network’s native token cannot be frozen at the smart contract level – unlike USDT.
On Ethereum in 2025-2026, the established route runs through decentralized stablecoins without freeze functionality, then into ETH, and onward through mixers. Tool selection at each step is deliberate – attackers systematically close every possible intervention point available to issuers and exchanges. After the mixer, funds move into fresh wallets and exit to fiat through OTC networks. Match Systems has examined the role of cross-chain infrastructure in laundering schemes in a separate analysis.
A stark illustration of the scheme’s speed: in December 2025, in one of the largest recorded address poisoning incidents, a victim lost $50 million in USDT – the entire path from receipt of funds to passing through a mixer took approximately 30 minutes. This is no longer improvisation; it is an executed algorithm.
Real Recovery Statistics: Match Systems Data
The question about recovery odds is the first one every victim asks. Match Systems answers it with data from its own caseload.
“Recovery” is defined as any partial or full outcome – funds blocked and subsequently returned. The figures below are approximate and depend on the specific circumstances of each case:
-
Response within the first hour – approximately 70% of cases with a practical outcome
-
Within the first four hours – approximately 60%
-
Within the first 24 hours – approximately 50%
-
After one month – approximately 20%
These figures are not a guarantee. They reflect the probability that a viable recovery path exists, depending on response speed. The final outcome depends on the funds’ routing path, the attacker’s operational sophistication, and law enforcement engagement.
How It Works in Practice: a Match Systems Case
A representative case from 2025-2026 – client identifiers withheld.
The victim contacted Match Systems within hours of the incident, having accidentally sent several hundred thousand dollars to an attacker’s address through a classic poisoning mechanism. The first step was immediate labeling of the attacker’s addresses as “stolen funds” in the AML databases used by exchanges for inbound transaction screening. Real-time monitoring ran in parallel.
A portion of the funds was successfully blocked at a service operating under AML compliance policies. Match Systems then prepared a complete analytical package for law enforcement on the client’s side: a blockchain investigation with transaction tracing, a visual asset-flow diagram, and templates for official information requests. Police submitted the necessary requests. The funds were returned to the client several months after the freeze.
This is the typical scenario when a victim acts quickly: not an instant result, but a managed process with a real outcome.
The Largest Public Recovery in This Category: $68M in One Week
On May 3, 2024, a victim sent 1,155.28 WBTC – approximately $68 million – to a spoofed address. One of the largest address poisoning incidents on record.
Match Systems, working jointly with exchange Cryptex, conducted negotiations with the attacker based on collected digital evidence – device fingerprints and behavioral patterns. Once the attacker understood that a clean exit was closed, they entered negotiations. On May 10, 2024, approximately 22,960 ETH was returned to the victim’s wallet. Total cycle: one week.
The key takeaway: deanonymization is not analytics for its own sake. It is a pressure instrument that changes the negotiating position.
Three Viable Recovery Tracks
Issuer-level freeze. If USDT has not yet been converted, it may be possible to block the attacker’s address at the smart contract level. The fastest path, but the window is minutes to hours. Once funds are converted to a decentralized stablecoin or ETH, this track closes.
Deanonymization and negotiation. This track worked in the WBTC case. It is realistic when the attacker is not a professional group with high operational security, and when the evidence base is sufficient for leverage.
Exchange-level block. Rapid address labeling increases the probability that AML filters trigger when the attacker attempts to deposit funds at an exchange. Less common – experienced groups avoid KYC-required services – but effective with a fast response.
What to Do in the First Minutes
The only factor a victim fully controls is speed.
– Immediately record the attacker’s address and the transaction hash
– Initiate labeling as “stolen funds”
– If USDT is involved – simultaneously submit a freeze request to Tether
– File a police report: without a criminal case, exchanges will not provide KYC information or freeze funds through official channels
– Do not engage in direct negotiations with the attacker before building an evidence base
A detailed step-by-step guide for post-theft response is available at matchsystems.com.
Every hour of delay reduces the probability of a result. Address poisoning is an attack with a response time window. Once assets are converted and passed through a mixer, that window closes.
Why the Wave Will Not Subside
The industrialization of this attack means its scale will grow in line with market growth. Infrastructure costs for attackers are negligible. Network upgrades that reduce fees automatically expand the attack surface – that is exactly what happened after Fusaka, and exactly what continues to happen in 2026.
The only factors that genuinely change the equation are victim response speed and the quality of labeling on the industry side. The faster attacker addresses enter AML databases, the more expensive each subsequent operation becomes for the perpetrators. Match Systems has detailed how this defense mechanism works in its analysis of blockchain labeling as a fraud countermeasure. It is not a solution to the problem – but it is what works right now.
Match Systems is an international blockchain intelligence and digital asset incident investigation firm.
@matchsystems_info | matchsystems.com
Disclaimer: This article is provided for informational purposes only. It is not offered or intended to be used as legal, tax, investment, financial, or other advice.